Qualys researchers have identified nine vulnerabilities in AppArmour that, they say, could let an unprivileged local Linux user gain root access and weaken container isolation on affected systems.
Dubbed CrackArmour, the issues relate to how the Linux kernel handles AppArmour security profiles. Qualys characterised the underlying pattern as a “confused deputy” problem, in which a low-privilege user influences a trusted process to perform an action that would normally be blocked.
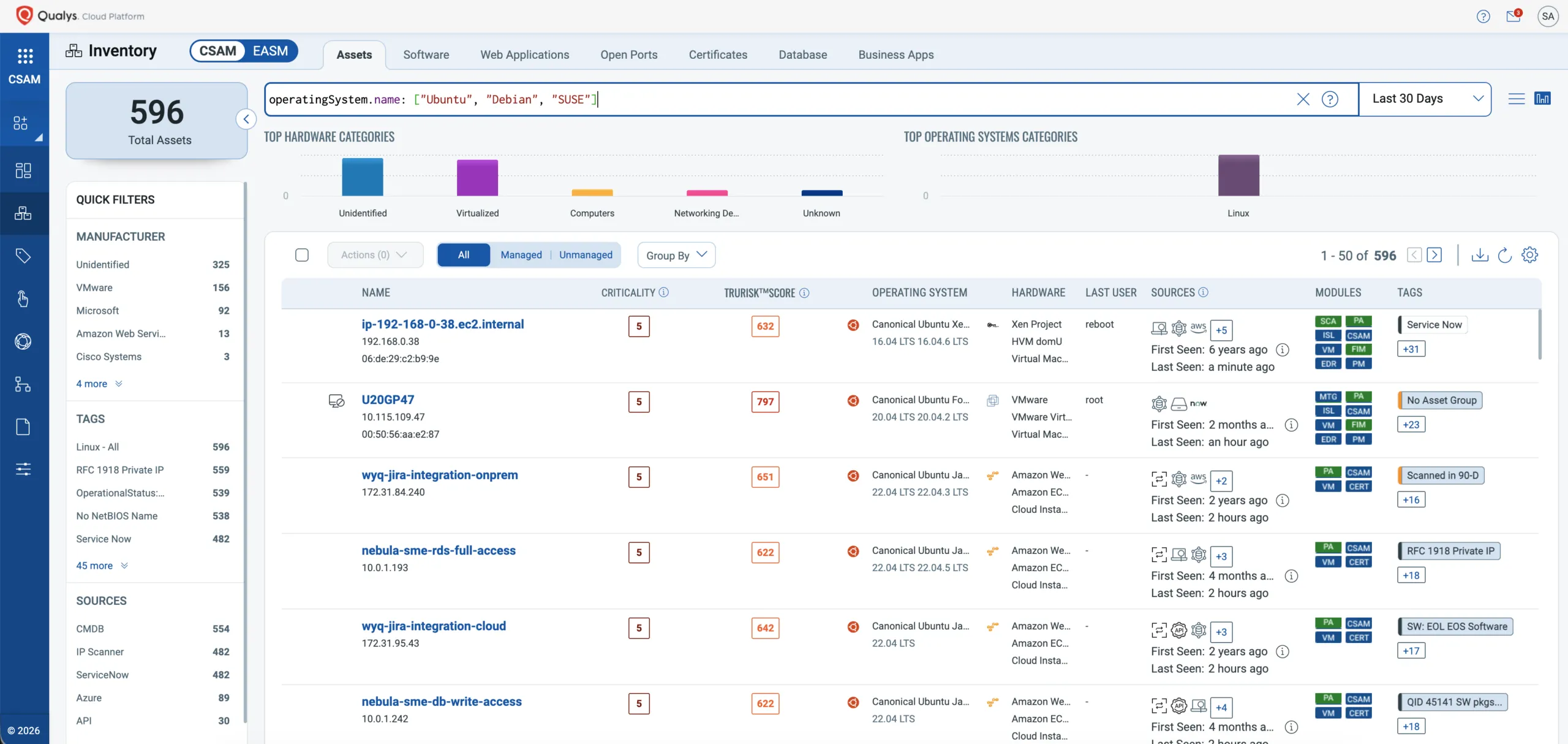
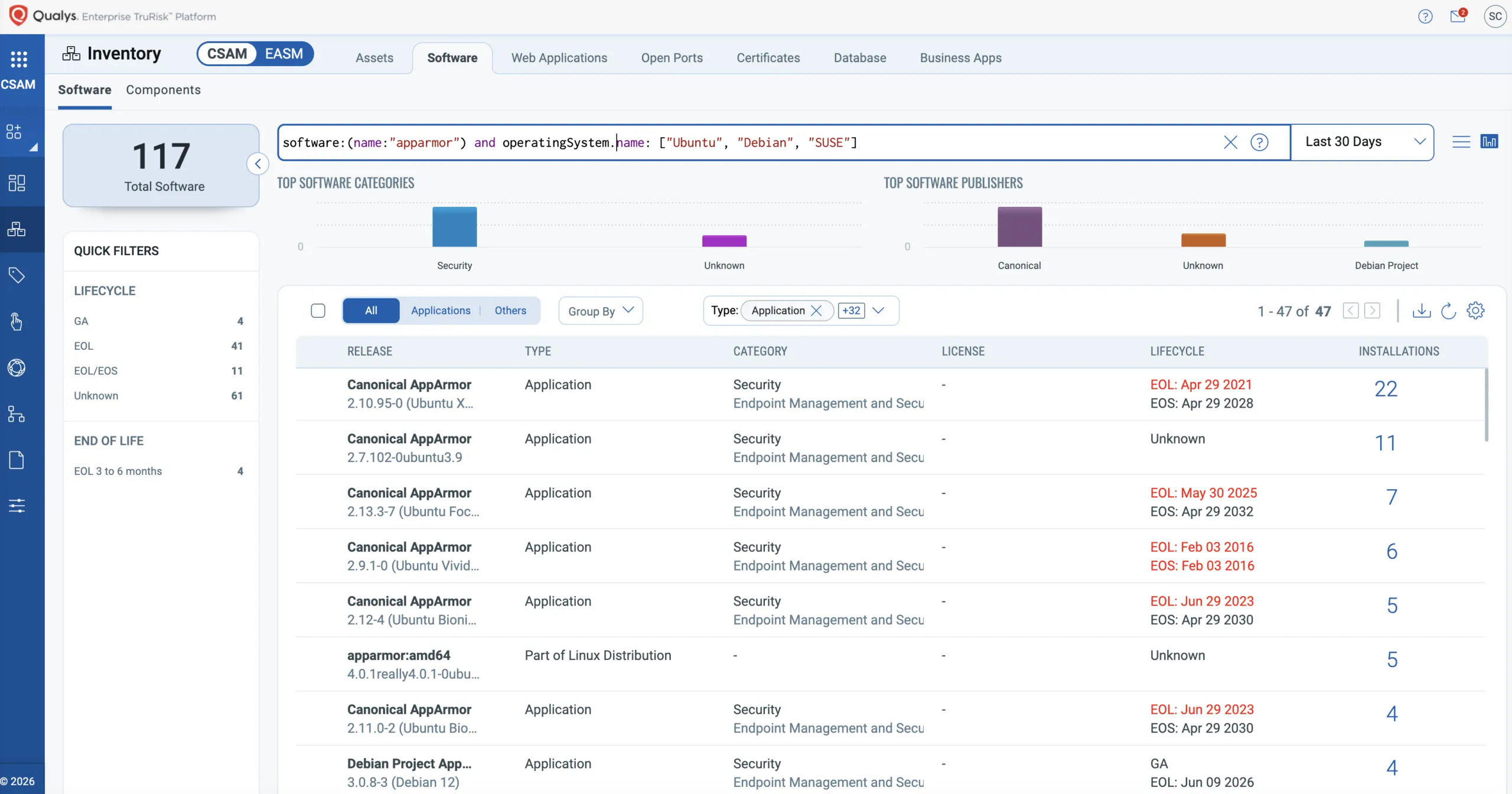
AppArmour is a Linux Security Module that enforces mandatory access control by applying profiles to applications. It is enabled by default on several major distributions, including Ubuntu, Debian, and SUSE, and is widely used in cloud and container environments for host hardening and workload confinement.
Qualys said the vulnerability set has existed since Linux kernel version 4.11, released in 2017. Its CyberSecurity Asset Management analysis found more than 12.6 million enterprise Linux instances with AppArmour enabled by default.
How it works
The reported weaknesses centre on pseudo-files used to load, replace, and remove AppArmour profiles. Qualys said an attacker could manipulate a privileged process to change profiles by writing to files under /sys/kernel/security/apparmor/, citing .load, .replace, and .remove as key interfaces.
Qualys said the flaws could bypass user-namespace restrictions and enable arbitrary code execution in the kernel. The advisory also describes denial-of-service risks: some removal paths can exhaust the kernel stack when profiles contain deeply nested subprofiles, potentially triggering a kernel panic and reboot in some configurations.
The write-up also outlines paths to local privilege escalation involving interactions with widely deployed components such as Sudo and Postfix. One example describes an attacker influencing mail-related behaviour to obtain a root shell. Another involves kernel memory misuse that could allow modification of /etc/passwd.
Qualys also raised concerns about container and namespace boundaries, warning that policy manipulation could let a user create more permissive namespaces on some systems. That could weaken isolation where distributions have restricted unprivileged user namespaces.
Patch urgency
Kernel updates are the primary remediation. Qualys said interim mitigations do not provide the same assurance as vendor fixes in kernel code and urged IT and security teams to expedite maintenance windows to deploy patched kernels.
The affected scope may extend beyond distributions where AppArmour is enabled by default. Any Linux distribution that integrates AppArmour and ships kernels from version 4.11 onward could be exposed, depending on configuration and patch level. Organisations should follow distribution-specific advisories for package versions and fixed kernels.
At the time of publication, the issues did not have CVE identifiers. Qualys noted that CVE assignment for upstream kernel issues typically follows fixes landing in stable kernel releases, and argued that defenders should not treat the absence of CVEs as a sign of lower risk.
Qualys said it has developed proof-of-concept demonstrations showing an exploitation chain for CrackArmour. It is not releasing exploit code publicly, but said the underlying mechanics remain available for independent validation by the security community.
Operational impact
The issues differ from remotely exploitable bugs because they require local access. That foothold could come from a compromised user account, a malicious insider, a vulnerable application that enables code execution as an unprivileged user, or a container escape attempt where the attacker already has limited rights on the host.
If AppArmour profiles protect network-exposed services, an attacker who can alter or remove those profiles can weaken defence-in-depth. Qualys cited examples such as removing profiles for services, including rsyslogd or cupsd. It also described a denial-of-service scenario in which a “deny-all” profile could be loaded for sshd, blocking legitimate administrative access.
Qualys advised monitoring for unexpected changes under /sys/kernel/security/apparmor/ as a potential indicator of exploitation. It also recommended prioritising patching for internet-facing assets and verifying AppArmour profile integrity after updates.
Qualys said its own products and platforms are unaffected. It also released a detection identifier for customers and pointed to a kernel version check as a way to assess exposure.
“These discoveries highlight critical gaps in how we rely on default security assumptions. CrackArmour proves that even the most entrenched protections can be bypassed without admin credentials. For CISOs, this means patching alone isn’t enough; we must re-examine our entire assumption of what ‘default’ configurations mean for our infrastructure,” said Dilip Bachwani, Chief Technology Officer at Qualys.

